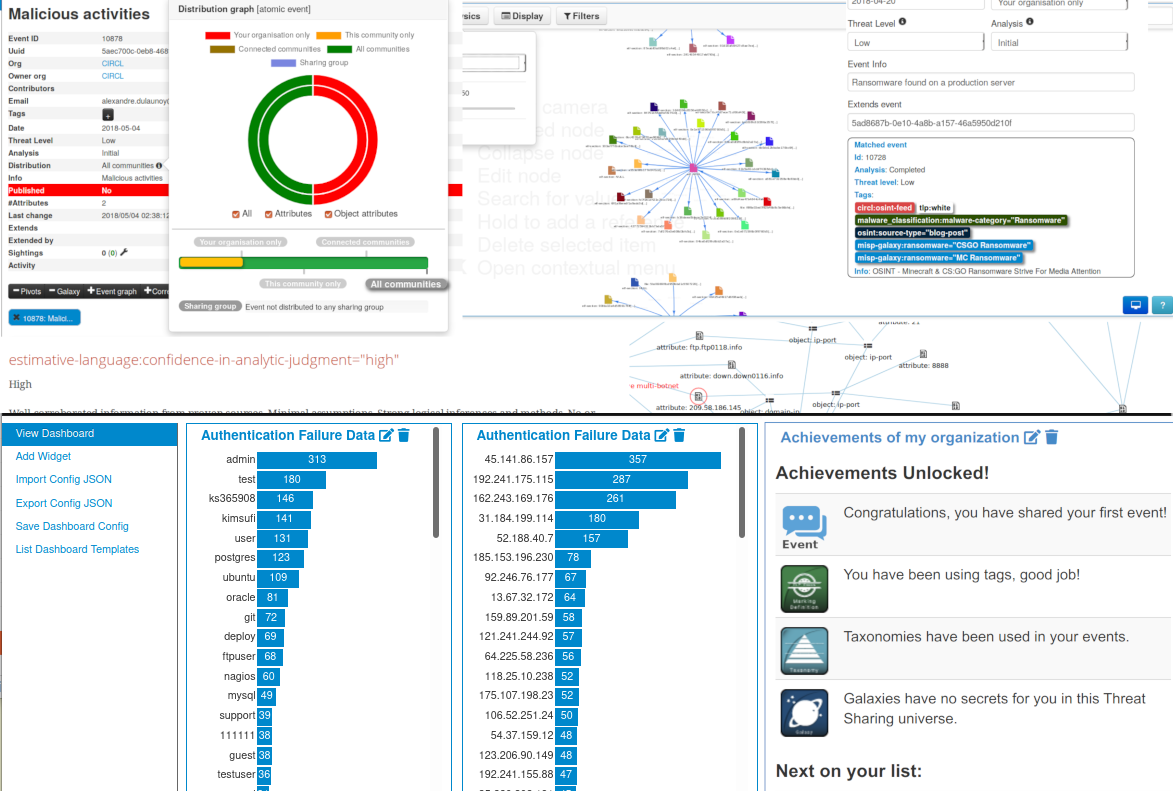
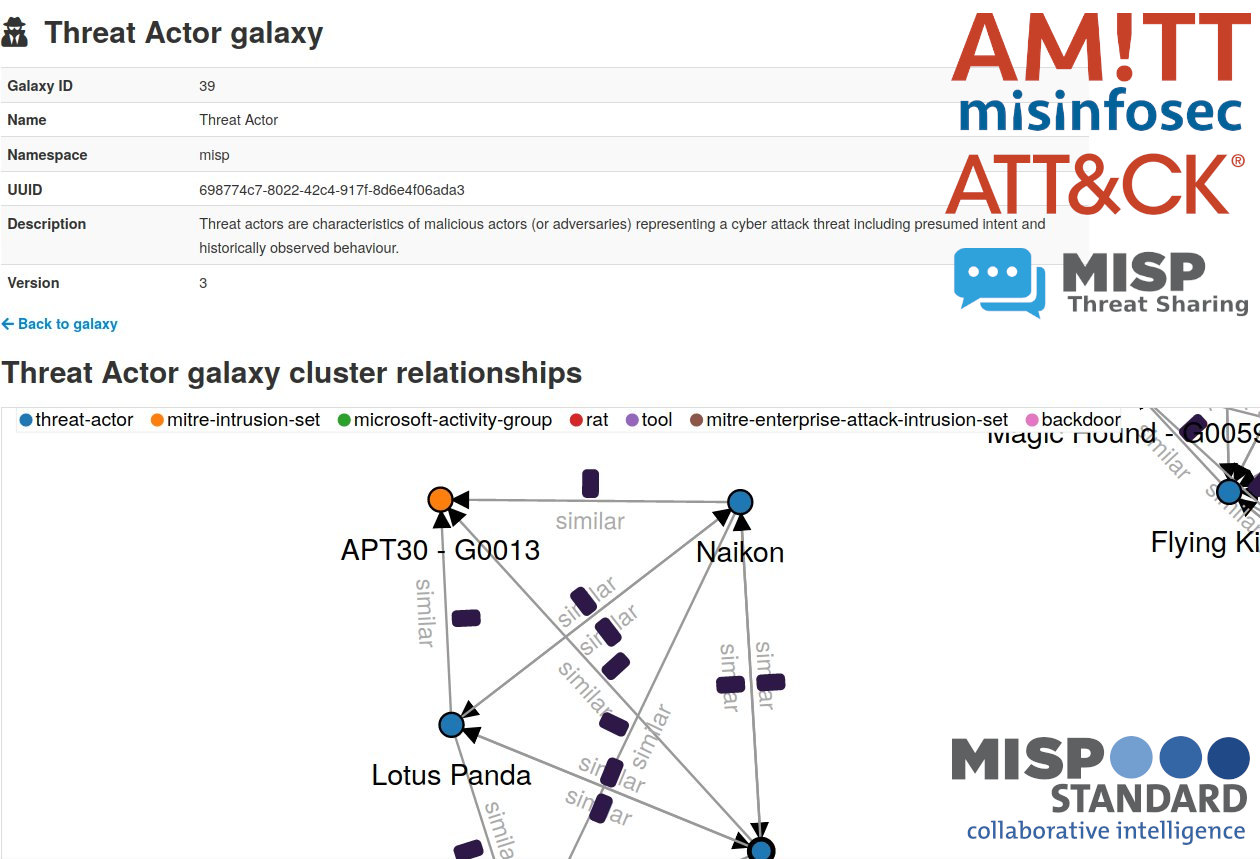
The MISP is an open source software solution for collecting, storing, distributing and sharing cyber security indicators and threats about cyber security incidents analysis and malware analysis. MISP is designed by and for incident analysts, security and ICT professionals or malware reversers to support their day-to-day operations to share structured information efficiently.
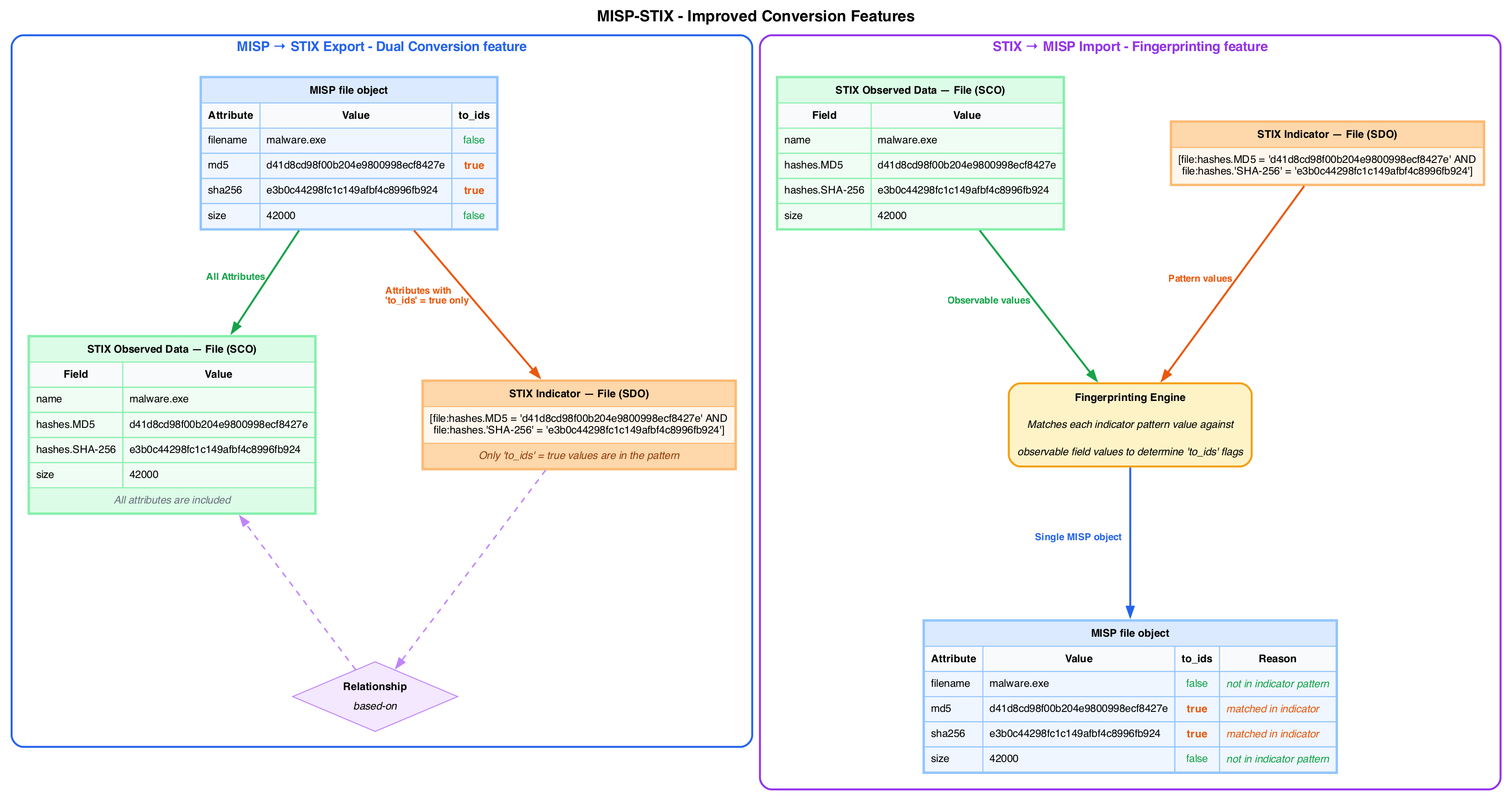
MISP v2.5.35: Decomposed Event Views, Overmind UI Enhancements, Security Hardening and MISP-STIX major update
The MISP v2.5.35 release introduces significant architectural improvements to the Event View, massive performance optimizations for attribute searching, and critical security hardening for installers. This version marks a major step forward in the “Overmind” UI project, transitioning toward a more modern, responsive user experience.