By Luciano Righetti March 13, 2026

MISP Workbench – First Release v1.0 (beta)
MISP Workbench is a powerful analyst-focused platform designed to tame the challenge of working with large volumes of threat intelligence at scale. It is capable of ingesting data from multiple origins — including MISP instances, external feeds, and other threat intelligence sources — and consolidates them into a unified workspace where analysts can actually get things done. At its core, MISP Workbench puts the analyst in control: query across your entire data corpus, enrich and process indicators, pivot between related intelligence, and push curated results back to MISP or downstream consumers — all from one place. Whether you’re triaging a large batch of incoming indicators, hunting for patterns across feeds, or preparing a finished intelligence product, MISP Workbench is built to cut through the noise and accelerate the workflow from raw data to actionable insight.
This first beta release marks the foundation of that vision — expect rough edges, rapid iteration, and a strong appetite for feedback.
Use Cases
Indicator triage at scale — When a large batch of new indicators arrives from multiple feeds, Workbench lets analysts query, filter, and correlate across the full corpus without jumping between tools or writing one-off scripts.
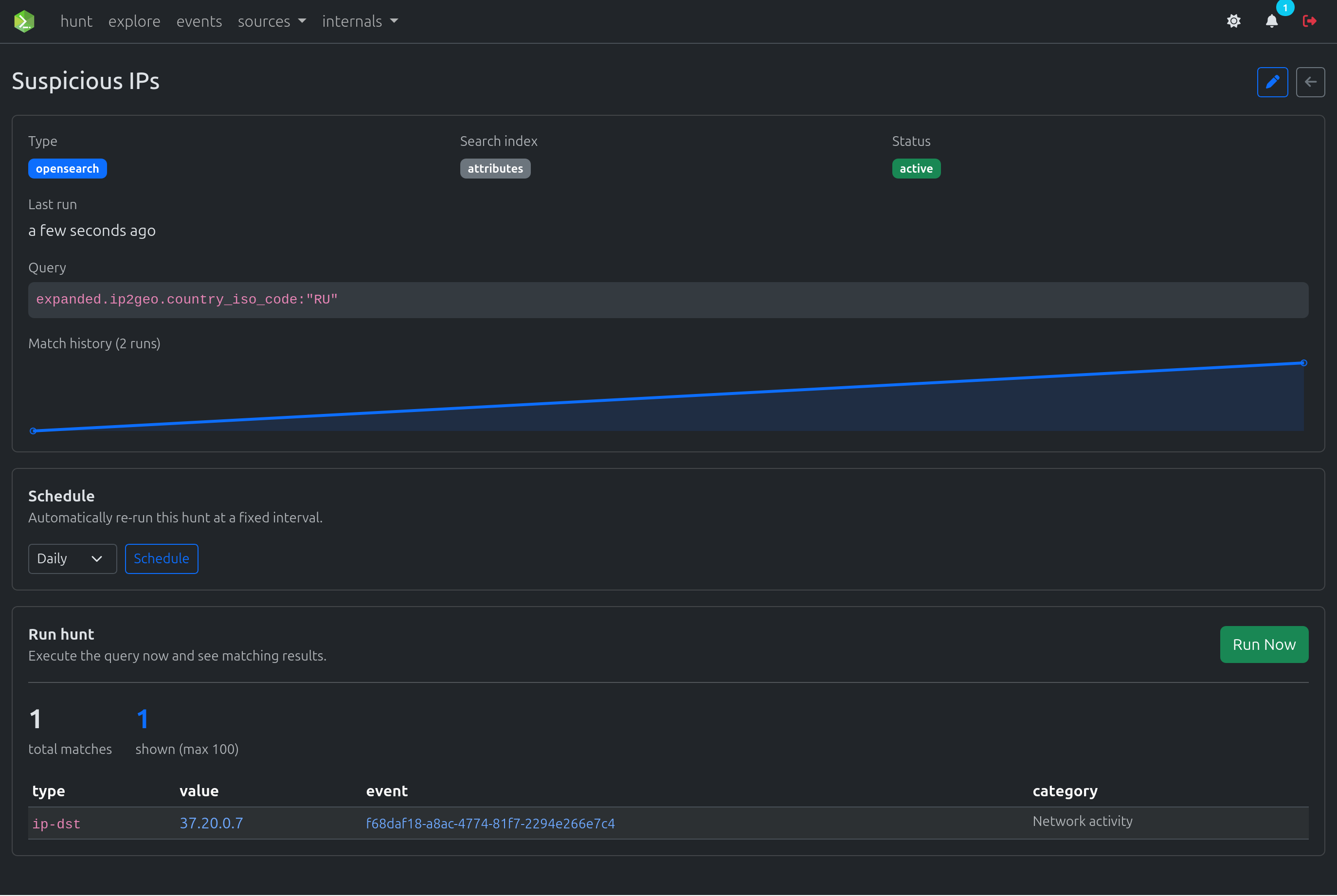
Threat hunting — Define saved searches (hunts) that run on a schedule and alert when matching indicators appear. Useful for persistent monitoring of specific adversary TTPs, infrastructure patterns, or emerging campaigns.
Feed consolidation and deduplication — Organisations running several MISP instances or subscribing to multiple commercial and open-source feeds can centralise ingestion, correlate overlapping data, and surface unique intelligence rather than processing the same indicators repeatedly.
IOC enrichment — Enrich ingested indicators through misp-modules (passive DNS, WHOIS, sandbox lookups, etc.).
Intelligence product preparation — Analysts can pivot between related indicators, build a curated dataset, and export a finished intelligence product without leaving the platform.
Who Is It For?
| Audience | Why Workbench helps |
|---|---|
| SOC / IR teams | Fast triage of incoming indicators against historical data; hunt for related infrastructure during an incident |
| CTI analysts | Centralised workspace for multi-source research, enrichment, and finished intelligence production |
| MISP operators | Offload heavy correlation and search workloads away from the core MISP instance |
| Red teams / researchers | Query large indicator datasets and cross-reference findings across feeds without running ad-hoc scripts |
Main Features
| Feature | Description |
|---|---|
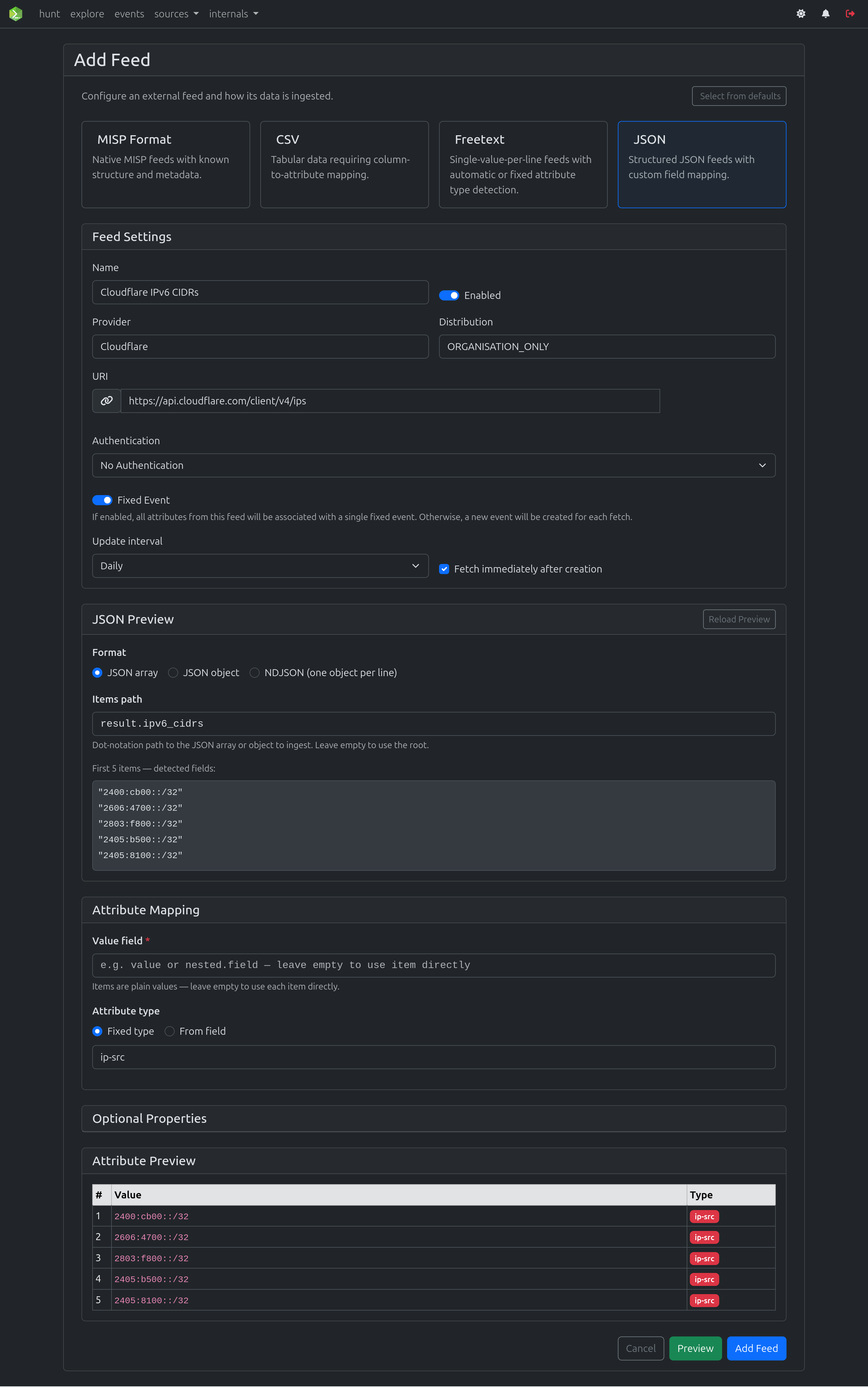
| Feed ingestion | Ingest MISP, CSV, JSON, and Freetext feeds on a schedule or on demand |
| Correlations | Batch and incremental correlation scans over indexed attributes |
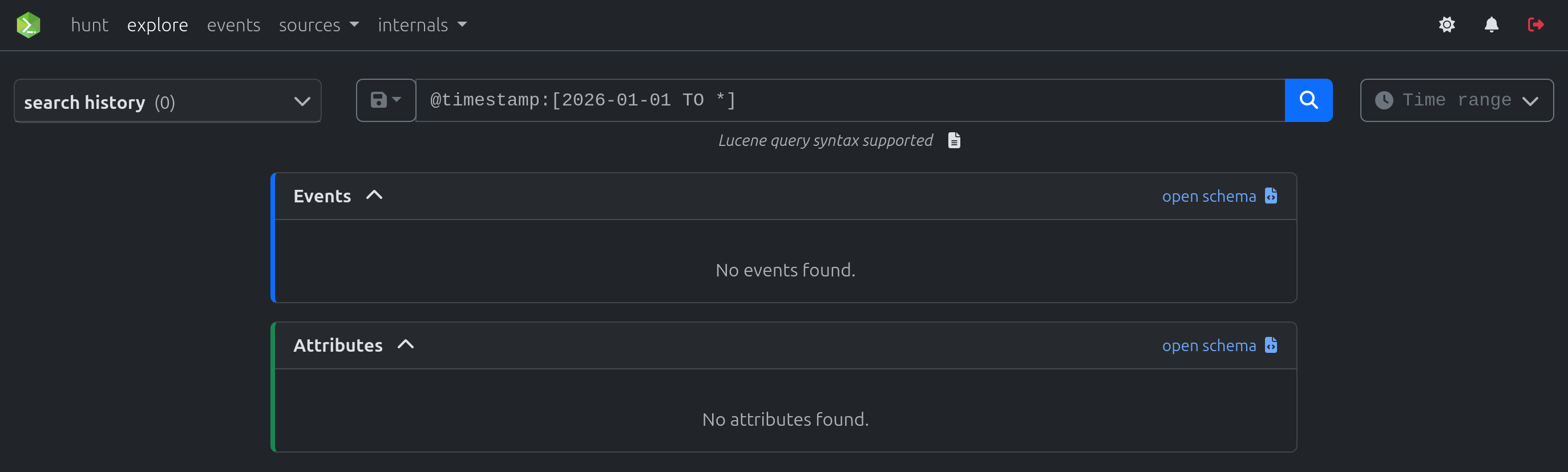
| Explore | Lucene queries against OpenSearch for fast indicator lookups |
| Enrichments | IOC enrichment powered by misp-modules |
| Hunt | Hunts are saved searches that run periodically and trigger alerts. |
| Notifications | Event-driven notifications processed by Celery workers |
| REST API | FastAPI backend with automatic OpenAPI documentation |
| Storage | Garage (S3-compatible) or local filesystem for attachments |
Get Started
- Repository: MISP/misp-workbench
- Release: beta-1.0
- Documentation: misp-workbench.readthedocs.io
Roadmap
Here is a glimpse of what is coming next:
- MCP Endpoints for LLM-Driven Querying of OpenSearch Data
- AI-assisted Lucene query-builder
- JA4+ correlations
- Flowintel Case Management Integration
- Something else? Let us know
Have a feature request, a bug report, or just want to share your experience? Drop some feedback — it helps shape what gets built next.
Screenshots